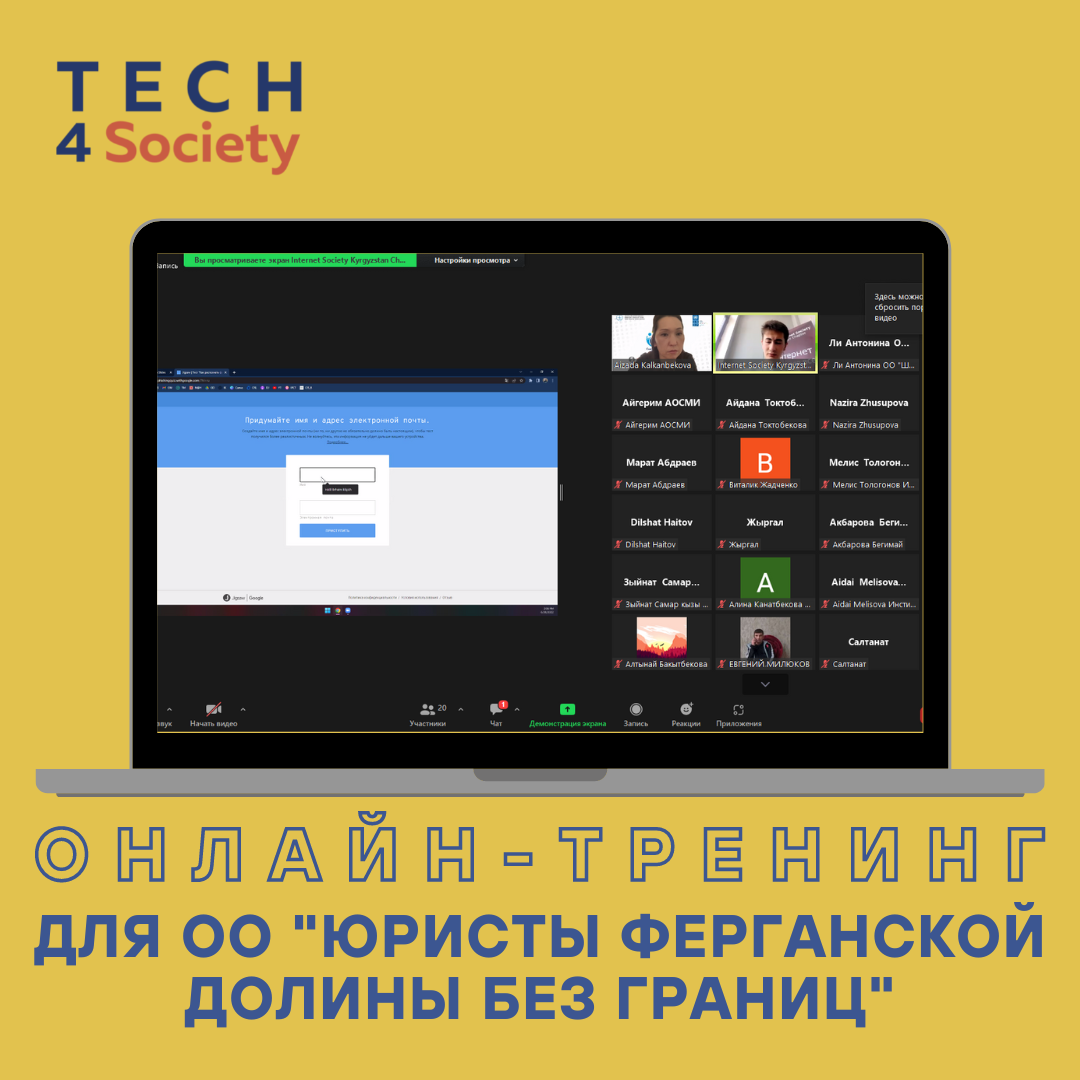
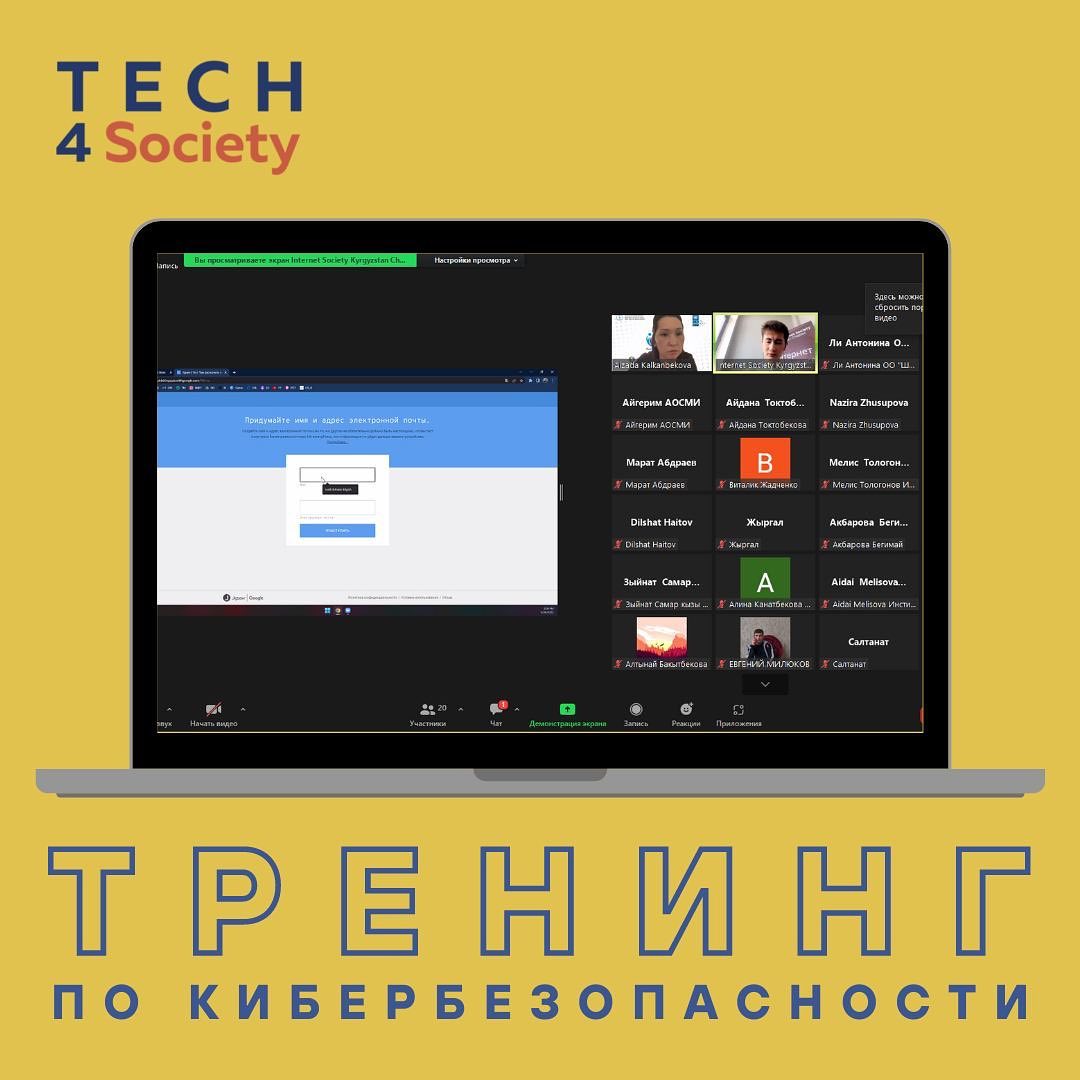
On June 30, 2022, within the framework of the Online Communities Accelerator project, an online Cybersecurity training was held, a guest speaker was a member of the Tech4Society team, Khalil Ibrahim Bilgich. He shared the basics of cybersecurity, Internet hygiene, safe online work and other useful and necessary information for non-governmental organizations. He also spoke about the project and shared contacts for contacting about the organization of training events on cybersecurity and the possibility of obtaining free scanning of web services for NGOs.
The participants of the event were: representatives of non-governmental organizations that work in various fields: the Association of Community Media, OF TB poeple, OF Tekayim, the Institute of Public Analysis, the Center for Civic Development, of Shoola Kol for Early Intervention.
Within the framework of the Online Communities Accelerator program, 11 coaching sessions are planned, as well as mentoring sessions to launch online campaigns. The project participants will pay attention to the topics that took place in the trainings and will use them when conducting online campaigns. From July 11, all participants will launch their online campaigns through various online platforms and social media.
_________________
Learn more about cybersecurity with us.
Protect yourself from cyber attacks, contact Tech4Society!